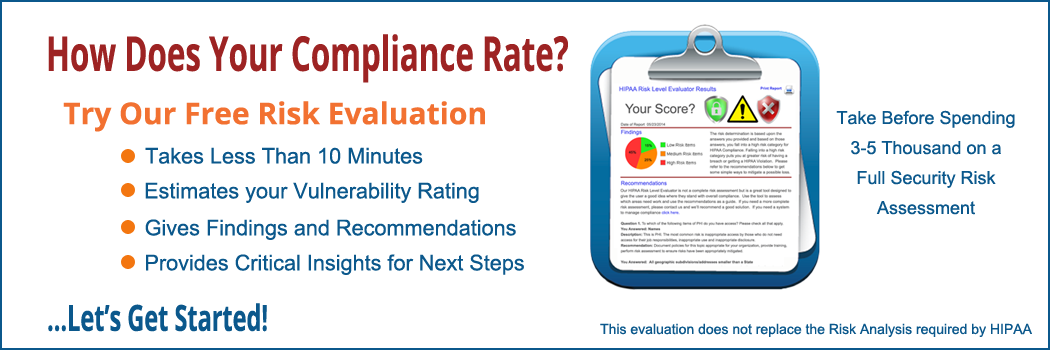
Below is our HIPAA Risk Level Evaluation. It has 31 privacy and security questions for you to answer and will take approximately 10 minutes to complete. The results will be made available immediately after the evaluation.
Please be sure to answer each question as truthfully and accurately as possible. Your answers are critical to the success of the overall report.
At the end we will ask for your name, company name and email and give you a detailed report immediately. The report is a graphical analysis that shows where you are with compliance. For each question answered, the report will give you a risk level, a detailed explanation and full recommendations based on how you answered each question. Enjoy!